🔐 Hawkins Lab Security: How Modern Cybersecurity Would Stop the Gate from Opening
How Stranger Things’ biggest breach could have been prevented with today’s technology
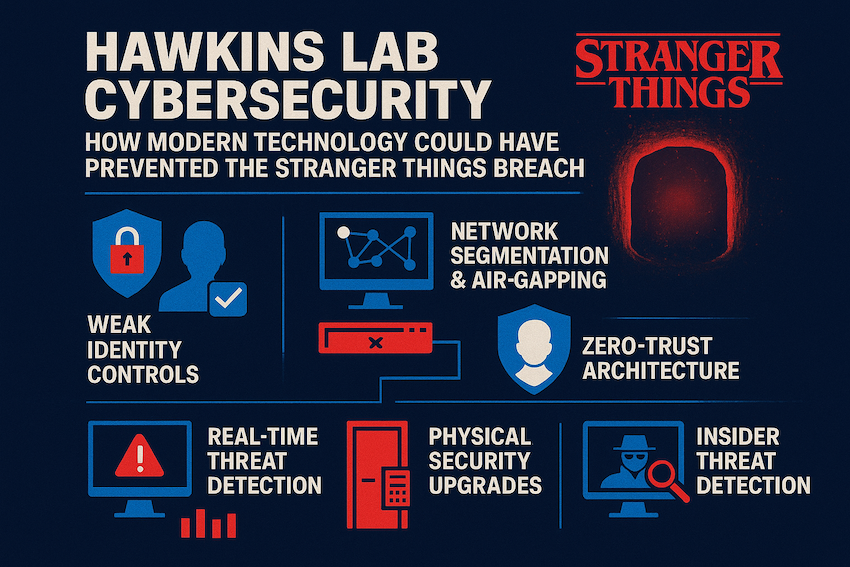
When the doors of Hawkins National Laboratory burst open and unleashed horrors from the Upside Down, it wasn’t just a supernatural failure — it was a textbook cybersecurity disaster. From poor access control to nonexistent threat monitoring, Hawkins Lab had all the red flags of a breached system waiting to happen.
If the same facility existed today, modern cybersecurity standards would have made the Gate incident significantly harder (if not impossible) to pull off. Let’s break down the failures — and how today’s tech could stop the chaos before it ever began.
🧪 1. Hawkins Lab’s Biggest Mistake: Zero Identity Controls
Personnel walk into high-risk areas with minimal verification. Badges are shown briefly, doors unlock easily, and sensitive experiments happen behind what amounts to glorified office security.
Today, this would never fly. Modern labs use multi-factor authentication (MFA) combined with biometric verification:
- 🔹 Fingerprint or palm vein scanners
- 🔹 Retina or facial recognition
- 🔹 Smart cards tied to real-time authentication systems
- 🔹 Continuous access monitoring
Why it matters: If a creature from another dimension can casually roam the facility, imagine what a determined human threat actor could do.
🧬 2. Air-Gapped Systems Would Have Controlled Everything
Everything behaved like a single insecure network — a nightmare for sensitive research.
- ✔️ Air-gapped networks: Critical systems isolated from the Internet entirely
- ✔️ Network segmentation: Zones prevent lateral movement if one device is breached
- ✔️ Industrial firewalls (OT security): Specialized protections used in nuclear and biotech labs
Result: The Gate’s activity, experiments, logs, and operational controls would be protected behind secure segments, making infiltration nearly impossible.
🏢 3. Zero-Trust Architecture Would Have Blocked Half the Show’s Problems
Hawkins Lab trusted everyone inside by default. Zero-Trust flips this concept: "Trust no one. Verify everything."
- ✔️ Every door, terminal, and sensor requires fresh authentication
- ✔️ No user gets full access — only exactly what they need
- ✔️ Continuous risk assessment shuts down suspicious behavior automatically
If Zero-Trust had existed in Hawkins, unauthorized movement or secret experiments would be flagged in minutes.
📡 4. Real-Time Threat Detection Would Have Caught the Breach Early
Even with monsters involved, unusual activity leaves trails: power fluctuations, sensor anomalies, EM readings, unusual badge scans, forced door openings, irregular lab equipment patterns.
Modern SOC tools like SIEM, SOAR, and ML-based anomaly monitoring would instantly detect the Gate’s distortions and alert security teams.
This is where the plot would have changed dramatically: The Demogorgon wouldn’t have roamed free undetected for days.
🔩 5. Physical Security Would Be Drastically Stronger
- ✔️ Blast-proof rooms
- ✔️ Smart locks with audit trails
- ✔️ Motion and thermal imaging sensors
- ✔️ Independent emergency containment systems
Automated barriers would isolate breaches instantly.
🧠 6. Insider Threat Protection Would Have Prevented Experiment Abuse
Today, insider threat platforms track behavioral anomalies, access misuse, off-hours data access, suspicious file transfers, and privilege escalations — shutting down secret projects that caused the Gate to open.
🧿 7. Predictive Analytics Could Have Detected the Gate Before It Opened
AI-driven anomaly detection interprets environmental data: EM spikes, non-human thermal signatures, pressure changes, air composition anomalies. A Gate forming would leave fingerprints in sensor data before anyone noticed.
🧩 Final Thoughts
The horrors of Stranger Things weren’t just caused by the Upside Down — they were caused by negligence, poor cybersecurity, and lack of modern defense systems.
- ✔️ Zero-Trust security
- ✔️ Biometric authentication
- ✔️ Air-gapped research networks
- ✔️ Real-time SOC monitoring
- ✔️ Automated containment systems
- ✔️ Insider threat detection
- ✔️ AI-driven anomaly prediction
And the Gate? It likely would have been detected, contained, and shut down long before anything crawled out.
Enjoyed this article?
Support the author — leave a quick review.
★ Make a ReviewRead our other articles
Privacy & Cookies
We use functional and analytics cookies to improve your experience. By continuing, you agree to our Terms of Service and Privacy Policy.












